Search
Items tagged with: InfoSec
I have a friend who is being harassed and threatened semi-anonymously via Facebook. She knows *who* it is, but Facebook and Police are characteristically being uselss.
I am kinda useless at this side of deanonymization, but does anyone have advice or resources for deanonymizing enough to get cops to move?
Well this was a pleasant surprise. Recorded a few years ago this was recently posted. I do remember it was like being in a bar in Vegas during DEF CON instead of a podcast, shooting the shit with an old friend. Thanks, @paulasadoorian it was a lot of fun.
https://www.scmagazine.com/podcast-episode/3277-hacker-heroes-mark-loveless-psw-vault

Hacker Heroes – Mark Loveless – PSW Vault
Exploring the Hacking Landscape with Mark Loveless, AKA SimpleNomad Dive into the intricate world of cybersecurity with our featured guest, Mark Loveless, widely known by his handle SimpleNomad.Security Weekly
4/4 🚀 🚀 🚀
Don’t miss out on this incredible opportunity! #GoTALER #onlinepayment #tech #technology #banking #finance #onlineshopping #freesoftware #openSource #developer #programming #privacy #DigitalRights #PublicCode #cybersecurity #infosec
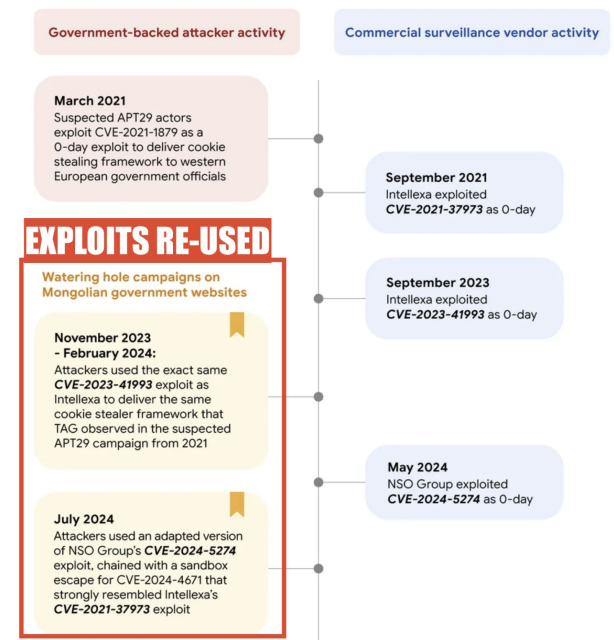
BIG: Russia caught reusing phone exploit strikingly similar to NSO Group's #Pegasus #spyware.
How did #APT29 get it after NSO used it?
Google isn't sure.
Ditto reuse of exploits from Intellexa.
But I warned Congress this would happen.
It says something about who NSO sourced it from, or that they can't control their code, or..
Whatever the case, the mercenary spyware industry is accelerating global cyber insecurity.
State-backed attackers and commercial surveillance vendors repeatedly use the same exploits
We’re sharing an update on suspected state-backed attacker APT29 and the use of exploits identical to those used by Intellexa and NSO.Clement Lecigne (Google)
In der IT kann es schon mal stürmisch werden! 🌪 Ihr wollt Cyberkriminelle von der Party ausschließen? Hier verraten wir euch, wie ihr eure digitalen Fenster und Türen absichert: 👉 https://www.bsi.bund.de/dok/131400
Ihr habt noch einen? Wir freuen uns eure liebsten IT-Flachwitze in den Kommentaren! 😜
#DeutschlandDigitalSicherBSI #IT #ITSicherheit #Sicherheit #CyberSecurity #ITSecurity #InfoSec #CyberCrime
As I'm attempting to do a write up on National Public Data breach, it keeps devolving. So I'm going to link to all the things, tips, sites I have used and hopefully that helps people navigate next steps. Please consider freezing your credit. It's not a cure-all but it can help.
Krebs has a good write up on it to start https://krebsonsecurity.com/2024/08/national-public-data-published-its-own-passwords/
I'll post all the things I've done as well. Should have blog up in in a few hours.

National Public Data Published Its Own Passwords
New details are emerging about a breach at National Public Data (NPD), a consumer data broker that recently spilled hundreds of millions of Americans' Social Security Numbers, addresses, and phone numbers online.krebsonsecurity.com
Important update from @briankrebs regarding the NPD breach:
https://krebsonsecurity.com/2024/08/national-public-data-published-its-own-passwords/
I hope quality reporting like this will foster a healthy discussion about how and to whom we entrust PII, but I won't be holding my breath.
In the article, Krebs provides links to sites that check
if your PII was exposed in this breach.
#infosec #cybersecurity #breach #pii

National Public Data Published Its Own Passwords
New details are emerging about a breach at National Public Data (NPD), a consumer data broker that recently spilled hundreds of millions of Americans' Social Security Numbers, addresses, and phone numbers online.krebsonsecurity.com

Jaw Dropping DNS Attack Vector Heavily Exploited in the Wild
Learn about the insidious DNS attack vector that threat actors are using to hijack domains from major brands, government institutions, and other organizations, large and small. Find out how to determine whether your domain name is at risk.Infoblox Threat Intel (Infoblox Blog)
Fuck Yeah, Astronomy!
"Researchers at the University of Hull recently unveiled a novel method for detecting AI-generated deepfake images by analyzing reflections in human eyes. The technique, presented at the Royal Astronomical Society's National Astronomy Meeting last week, adapts tools used by astronomers to study galaxies for scrutinizing the consistency of light reflections in eyeballs."
Astronomers discover technique to spot AI fakes using galaxy-measurement tools
Researchers use technique to quantify eyeball reflections that often reveal deepfake images.Ars Technica
Did you know #Project2025 calls for “the entirety of the CISA #Cybersecurity Advisory Committee should be dismissed on Day One.” (page 155).
If you like being able to use computers (or do anything with organizations that use computers, including have your vote counted in elections) that’s a very bad idea.
Threat actor #emo, who has the nerve to claim he answers to God while robbing people, said "unsecured API endpoint used to steal the data provided an easy way to verify each impacted user's email address, name, and phone number."
More than 400,000 #Life360 user phone numbers leaked via unsecured API https://www.bleepingcomputer.com/news/security/over-400-000-life360-user-phone-numbers-leaked-via-unsecured-android-api/ @BleepingComputer @serghei #infosec #cybersecurity
It has been a while since I’ve written about Avast, so today I give you “How insecure is Avast Secure Browser?”
https://palant.info/2024/07/15/how-insecure-is-avast-secure-browser/
Note: This isn’t a vulnerability disclosure, merely an overview of problematic design decisions.
TL;DR from the article: I wouldn’t run Avast Secure Browser on any real operating system, only inside a virtual machine containing no data whatsoever.
Some highlights:
- Eleven pre-installed browser extensions but only two visible to users.
- Two extensions unnecessarily relax Content-Security-Policy protection.
- One of these two extensions also requesting all privileges possible, despite not actually using them.
- Two extensions accept messages from any other extension and any Avast website, the latter without enforcing HTTPS connections.
- One of these extensions, Privacy Guard (sic!), will expose information about your browser’s tabs via that messaging interface and provide updates as you browse the web.
- The “onboarding” experience is designed as an extremely flexible way to nag you into using products that benefit Avast financially.
- To make this “onboarding” work, the browser exposes internal APIs to a number of Avast domains that a huge number of third parties can put content on. Not only can each of these third parties abuse this access, a single XSS vulnerability will extend the access to any website on the internet (no effective CSP protection).
Enjoy!
#avast #avg #avira #ccleaner #securebrowser #infosec

How insecure is Avast Secure Browser?
Another look into Avast Secure Browser shows a massive attack surface, with some issues mentioned five years ago only partially addressed, all while new ways to attack the browser have been added.Almost Secure
Hey, has anyone written on what blue teamers and CTI folk should do to protect themselves from retribution by bad actors? What steps to take, services to use, etc other than basics like credit freeze?
CISA Red Team’s Operations Against a Federal Civilian Executive Branch Organization Highlights the Necessity of Defense-in-Depth
"...the Cybersecurity and Infrastructure Security Agency (CISA) conducted a SILENTSHIELD red team assessment against a Federal Civilian Executive Branch (FCEB) organization...."
includes red team TTPs, defense activity, and lessons learned.
https://www.cisa.gov/news-events/cybersecurity-advisories/aa24-193a
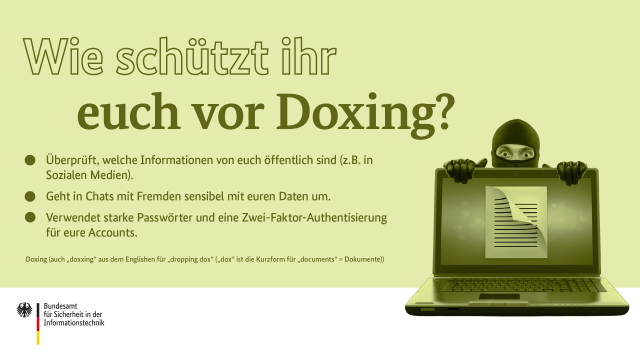
Doxing kann euer Leben auf den Kopf stellen: Zum Beispiel, wenn plötzlich eure Adresse öffentlich einsehbar ist und ihr euch dadurch bedroht fühlt oder unerwünschte Post bekommt. Seid darum vorsichtig mit persönlichen Informationen online und haltet sensible Daten geheim. Wir zeigen heute, wie es geht! 🔒
#DeutschlandDigitalSicherBSI #IT #ITSicherheit #Sicherheit #CyberSecurity #ITSecurity #InfoSec #CyberCrime